Sunday 02 February 2025
Watermarking is a technique used to protect digital content by embedding a unique identifier into the data. This identifier, known as a watermark, can be used to verify the authenticity of the content and track its ownership. However, as technology advances, hackers have developed methods to remove or evade watermarks, making it difficult for content creators to ensure their work is protected.
A recent study has shed light on the effectiveness of various watermarking methods against different types of attacks. The researchers tested several popular watermarking algorithms, including HiDDeN, StegaStamp, RivaGAN, and MBRS, against a range of attack methods, including optimization-based attacks, embedding attacks, and surrogate detector attacks.
The study found that while some watermarking methods were more resilient to certain types of attacks, none were completely foolproof. The researchers discovered that the effectiveness of a watermarking method depended on several factors, including the architecture of the encoder and decoder, the type of attack used, and the quality of the watermarked image.
One surprising finding was that HiDDeN, a popular watermarking algorithm, was vulnerable to optimization-based attacks. This is because HiDDeN relies heavily on convolutional neural networks (CNNs) to embed the watermark, which can be easily manipulated by an attacker using optimization algorithms.
On the other hand, StegaStamp and RivaGAN showed more promise against various types of attacks. These algorithms use different approaches to embed the watermark, such as using a U-Net style architecture or attention mechanisms, which make them more difficult to evade.
MBRS, another popular watermarking algorithm, was found to be robust against most attack methods, but its effectiveness depended on the alignment of its encoder and decoder architectures with those of the surrogate models. The study found that aligning MBRS’s encoder and decoder architectures improved its resilience to attacks, making it a more effective watermarking method.
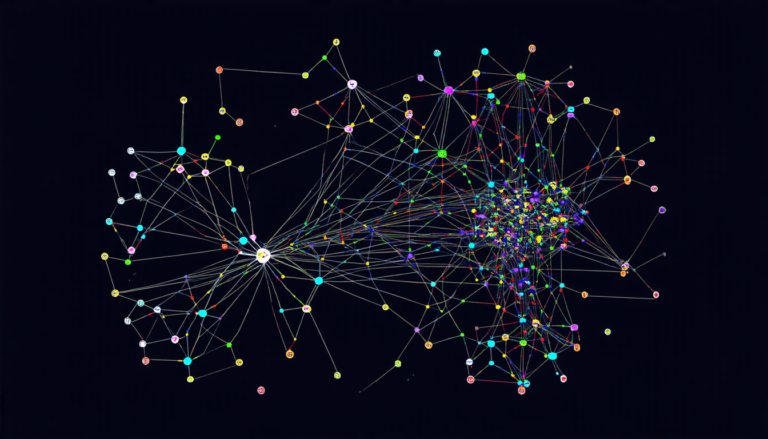
The researchers also tested a naive transfer attack using OFT (one-off trial) on different target models with k = 1. This experiment showed that only when the target model matched the surrogate model did the attack succeed. This highlights the importance of aligning the architectures of the encoder and decoder in a watermarking algorithm to ensure its effectiveness.
In summary, the study demonstrates that while watermarking methods are not foolproof against attacks, some algorithms show more promise than others.
Cite this article: “Watermarking Techniques Under Attack: A Study on Effectiveness Against Different Types of Attacks”, The Science Archive, 2025.
Digital Content, Watermarking, Authentication, Ownership, Hacking, Algorithm, Attack Methods, Convolutional Neural Networks, Cnns, Optimization-Based Attacks